Private 4G and 5G networks are rapidly becoming mainstream. This isn’t news.
But
from recent conversations, client engagements and events, it’s becoming
increasingly clear that many don’t quite grasp how private cellular
use-cases are segmented – and why it’s going to get even more complex in
the next 2-3 years.
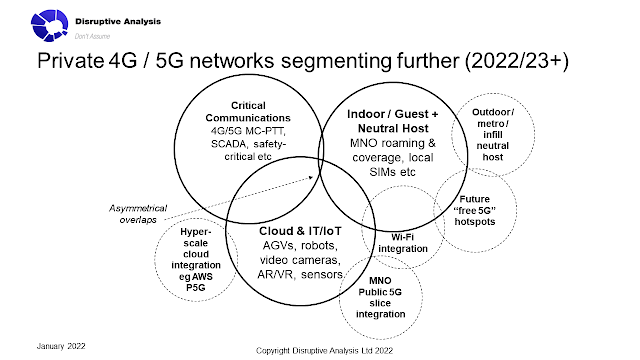
In reality, this isn’t really “a market” in a singular sense. It’s currently at least three separate and distinct markets, with only minimal overlap at present. The main common thread is the deployment of cellular (3GPP 4G/5G) networks by non-MNOs.
A
common fallacy involves talking about “vertical industries” as the main
way to divide up the sector. But that doesn’t really work, as any given
vertical has dozens of sub-categories and hundreds of potential
applications and deployment scenarios. For instance, the “energy
vertical” covers everything from a gas station, to an offshore windfarm,
a 1000km pipeline or an oil-futures trading floor in a financial
district.
Verticals are useful ways to divide up sales and
marketing efforts, and make sense for cohesive reports, papers or
webinars, but also blend together elements of three very different markets for private 4G/5G:
- Critical communications networks
- Indoor mobile phone networks
- Cloud and IT/IoT networks
It is worth discussing each of these in turn.
Critical communications networks
These
have made up the bulk of major private network deployments over the
last 5-10 years. They are typically deployed for utilities, oil &
gas, mining, public safety, airports and military purposes. Often, they
are used in rugged environments, for human communications (typically
push-to-talk), as well as in-vehicle gateways and specific automation
systems such as remote sensors and monitoring systems. The specialised
GSM-R system for railways fits in this category as well.
Usually,
they are replacing alternatives such as private mobile radio (PMR),
TETRA and microwave fixed-links. They have typically been packaged and
deployed by specialist integrators for sectors like oil-rigs or
field-deployment by military units. There is limited “replicability”.
They vary widely in size, from a single portable network for public
safety, up to a national network for a utility company.
There is
little need for interconnection with public mobile networks; indeed it
may be specifically avoided in order to maintain isolation for optimal
security and “air-gapping” for critical applications.
Most are 4G,
reflecting mission-criticality and its frequent need for proven, mature
technology and wide product availability. 5G is however used in certain
niches and is being tested widely, although the most useful features
will only arrive when Release 16/17 versions are commercialised in the
next few years.
Indoor mobile phone networks
This includes
some of both the oldest and newest deployments. Early local private
2G/3G networks essentially used GSM phones and thin slices of
light-licensed/unlicensed spectrum to replace DECT cordless phones in a
few markets – notably the UK, Netherlands and Japan.
They could
also work with multi-SIM phones to blend public and private modes. I
first saw an enterprise-grade GSM picocell in 2001, and an on-premise
core network box in 2005. There are still several thousand such networks
around, including ones updated to 4G and some that run on ships or
onboard private jets.
More recently, there has been growing
interest in using private 4G/5G to create neutral host networks for
in-building, or on-campus coverage. There are multiple models for
neutral host (I’ve counted around 10-15 variations), with some needing a
full local network with its own spectrum and core, and others just
relying on the tenant MNOs’ active equipment. In the US, CBRS-based
options may turn out to be among the more sophisticated.
Whether
used to support public MNOs more effectively than alternative indoor
systems such as DAS (distributed antenna systems), or perhaps for
linking to a UC / UCaaS system for enterprise voice, the main use-cases
are for phones. They are almost always deployed for a single building or
campus.
This segment is the most likely to require
interconnection with the public mobile infrastructure, as well as
supporting normal “phone calls” rather than push-to-talk voice.
Cloud and IT/IoT network
This
category of private cellular is probably receiving the greatest
attention from many newcomers to the sector, as well as external
observers such as analysts and journalists.
It ties in with many
of the newest trends around cloud and edge-computing, AI and machine
vision in factories, robots and AGVs in warehouses, security cameras and
more general IoT / smart building use-cases. It aligns with many of the
"transformation" projects in IT, plus some parts of the OT (operational
technology) space such as smart manufacturing.
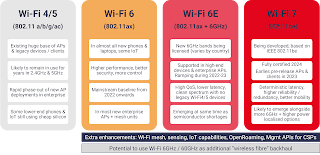
As such, it tends
to be viewed as a complement – or alternative – to other IT-type network
technologies like Wi-Fi and fibre-based ethernet. And given that many
of the use-cases have a heavy cloud (or at least multi-site WAN)
orientation, there is more acceptance of virtualisation of cores and
perhaps in future the RAN.
This is currently the area with the
greatest amounts of experimentation and innovation – although actual
large-scale operational deployments are still relatively few. There is
more focus on 5G than 4G, although that might change as executives learn
more about the practicalities and economics. Vendors often orient on
the soundbite that "private 5G should be as easy as Wi-Fi".
There
is a major focus on automation, replicability and ease-of-use. This was
exemplified by the recent AWS Private 5G announcement, which seems
squarely aimed at this segment.
However, there is perhaps a divide
opening between the IT-type scenarios (where it can be seen as a sort
of enterprise Wi-Fi-on-steroids vision) and OT deployments in which it
gets embedded into larger industrial automation or other systems, such
as factory robots or dockside cranes. In the latter scenarios we can see
companies like Siemens integrating cellular into their wider systems,
just as they have historically used Wi-Fi/WLAN and fibre.
Although
the main focus is on building / campus networks for this model, it may
also extend to larger domains such as smart cities, as well as
multi-location users such as retail chains.
There is some
overlap with the critical communications segment, but that is fairly
rare at the moment, especially given the lesser role (and trust) of
public cloud in many of those areas.
In addition, there is a fair
amount of talk about interconnection with the public mobile network
(especially where telcos are acting as vendors), but in reality, that's a
secondary consideration that doesn't go much beyond a PowerPoint slide
for now. There are certain exceptions which are interesting, but they're
far from typical.
Conclusions and the Future of Private Networks Segmentation
At
present, the "private 5G market" is actually at least three separate
markets. And it's mostly about private 4G rather than 5G. Critical
communications networks, indoor mobile phone networks and cloud/IT/IoT
networks are largely distinct in terms of motivations, channels,
economics, devices and applications. There is much less overlap than
many observers expect.
(There are also smaller adjacent sectors such as community networks, 4G/5G-based FWA and other specialities).
But
over the next 1-2 years, we can expect the three bubbles on the Venn
diagram to overlap more – although asymmetrically. Critical and
cloud/IoT networks will start to become hybridised. Critical 4G/5G
networks in mines or utility sites will start to support extra IT-like
applications, for instance (although that probably won't need formal
network slicing).
Some enterprise private cellular networks will
examine adding neutral-host and inbound roaming or interconnect from
public MNOs' subscribers – although there are assorted regulatory and
security/operational hurdles to address.
There won't be much
overlap between critical networks and neutral/guest cellular, though.
Nobody's smartphone will be roaming from their normal consumer 5G
network onto the utility company's private infrastructure, I think. A
few employees' devices might have special arrangements though.
But
we will also see the emergence of a number of additional bubbles on the
chart, some of which are more like "quasi-private" models, such as
outdoor neutral host networks, selling wholesale capacity to MNOs. There
will be various forms of Wi-Fi integration (but probably less than many
expect / want). And we will undoubtedly see maturity of both
cloud-delivered private cellular like AWS's, and (belatedly) some sort
of MNO-based network slice integration.
And if you want an
"outlier" to ponder, consider the potential for grassroots private
"consumer-grade" 5G. There's a lot of hype about things like Helium's
decentralised and blockchain-based model, but I'm deeply sceptical of
this (that's for another post, though). More likely is the emergence of a
true Wi-Fi hotspot approach, where we start to see lightweight "free
5G" options, using unlicensed (or maybe CBRS GAA) spectrum, with a cheap
core and small cell. Scan the QR code next to the barista to download
your eSIM, and you're good to go….
The bottom line is that the
private 4G/5G market is complex and nuanced. Market statistics
frequently combine everything from a nationwide utility's or railway's
critical infrastructure, to a few small-cells connecting up digital
signs in a mall car-park. It's easy to assume it's all about
millisecond-latency robots zipping about factories, rather than a
security guard with a handheld radio, or indoor network coverage for a
hotel.
Operators, vendors, enterprises and governments need to
delve a bit more deeply than just talking about "verticals" for private
cellular, or else they risk making errors with their product portfolios
or regulatory direction.
Dean Bubley (@disruptivedean) is a
wireless technology analyst & futurist, who advises a broad range of
companies and institutions active in the 5G, Wi-Fi and cloud
marketplaces. He has covered private cellular networks for more than 20
years. He is a regular speaker and moderator at live and virtual events. Please get in touch on LinkedIn or via information AT disruptive-analysis DOT com for advisory or speaking requests.
#Private5G #Private4G #CriticalCommunications #5G #IoT #IIoT #Cloud #WiFi #verticals